Introducing Redgate Monitor’s new estate discovery feature
This year we’ve been expanding Redgate Monitor’s capabilities around the theme of Estate Management and we’ve just released a new capability – the discovery of on-premises SQL Servers and instances.
We started on this journey with basic instance configuration observability and alerting earlier this year. While gathering feedback and finding ways to improve our new configuration features, we worked on and released an Instance Discovery Tool as a preview feature.
We believe this tool is useful for DBAs who look after particularly dynamic estates where instance and server deployments aren’t always made in code and are not always well communicated. It can also speed up the first installation of Redgate Monitor in large estates.
We’d love your feedback on it and ways you think it could be improved – contact us if you’d like to leave feedback or do it in the app.
How can I use it?
Any Redgate Monitor administrator can use the capability. Firstly, you’ll need to update your Redgate Monitor to the latest version to enable and use the new Find SQL Server instances feature. Then go to Configuration -> Instance discovery and enter the domain you want to query. You can narrow it down to a subset of the domain by supplying an LDAP path.
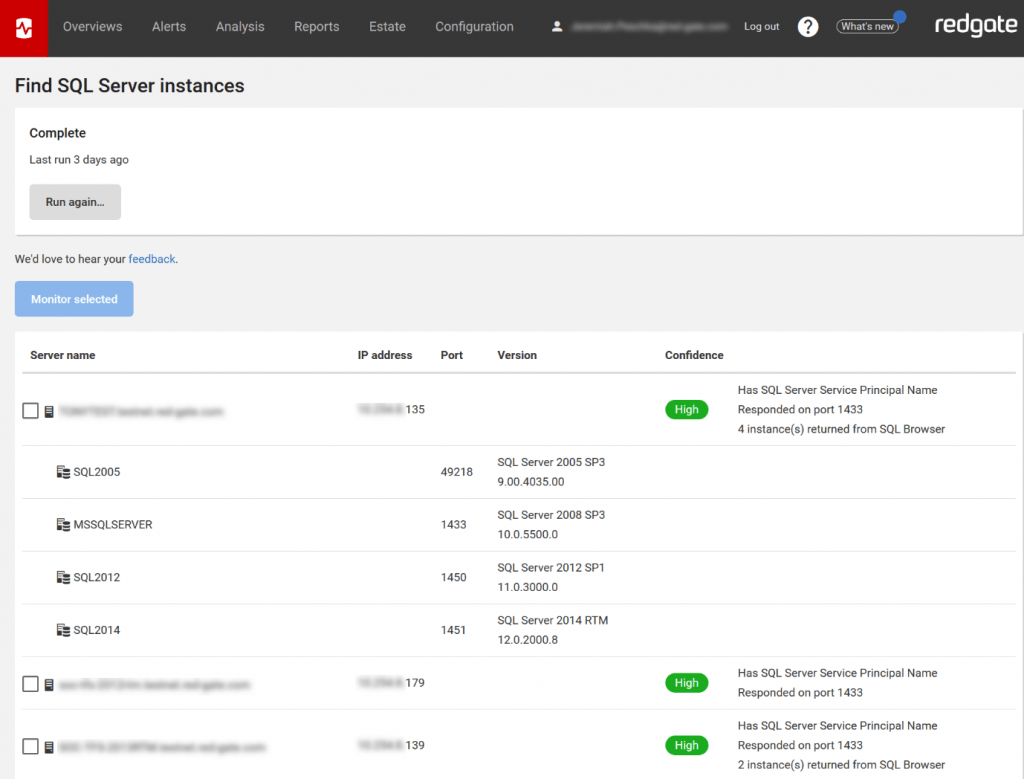
After looking for SQL Servers on your network, Redgate Monitor will display all of the servers and instances found and give you the option to monitor them:
A safe approach to Instance discovery
From early research, it was clear that we needed a safe approach to instance discovery that minimized the risk of Redgate Monitor appearing as a malicious activity on the network.
We decided to use Active Directory to obtain a list of devices instead of IP range scanning. The presence of a SQL Server is then optionally tested by trying to connect to a standard SQL Server port (by default, 1433) and by querying SQL Browser.
We believe this is a safe way to discover servers that has minimal network impact. Infrastructure stakeholders should still be consulted before use, however.
What will the process find?
Our instance discovery process reports devices marked as SQL Servers in Active Directory, SQL Servers listening on the default port, and instances with the SQL Browser service active.
Things it does not do
We decided not to do IP range sniffing or authenticate against any of the servers or instances the process finds. These actions look a bit like a security anomaly, and we don’t want your security staff to think of Redgate Monitor as malicious.
As a result of being conservative, the information the process can gather is limited to presence, version, and build number. We’re now exploring the possibility of authenticating against the discovered servers to retrieve more information about them.
If you have any ideas, observations or opinions on how you think our new estate discovery feature could be improved, please contact us or provide feedback in the app.
If you’re new to Redgate Monitor and would like to see how it can help you monitor large, mixed estates more effectively, you can also download a fully-functional 14-day free trial, or try our live online demo environment.
Tools in this post
Redgate Monitor
Real-time multi-platform performance monitoring, with alerts and diagnostics








Loading comments...