Articles
Articles



Security vs speed in databases
Subscribe to the Simple Talk newsletter

Accelerate your database learning
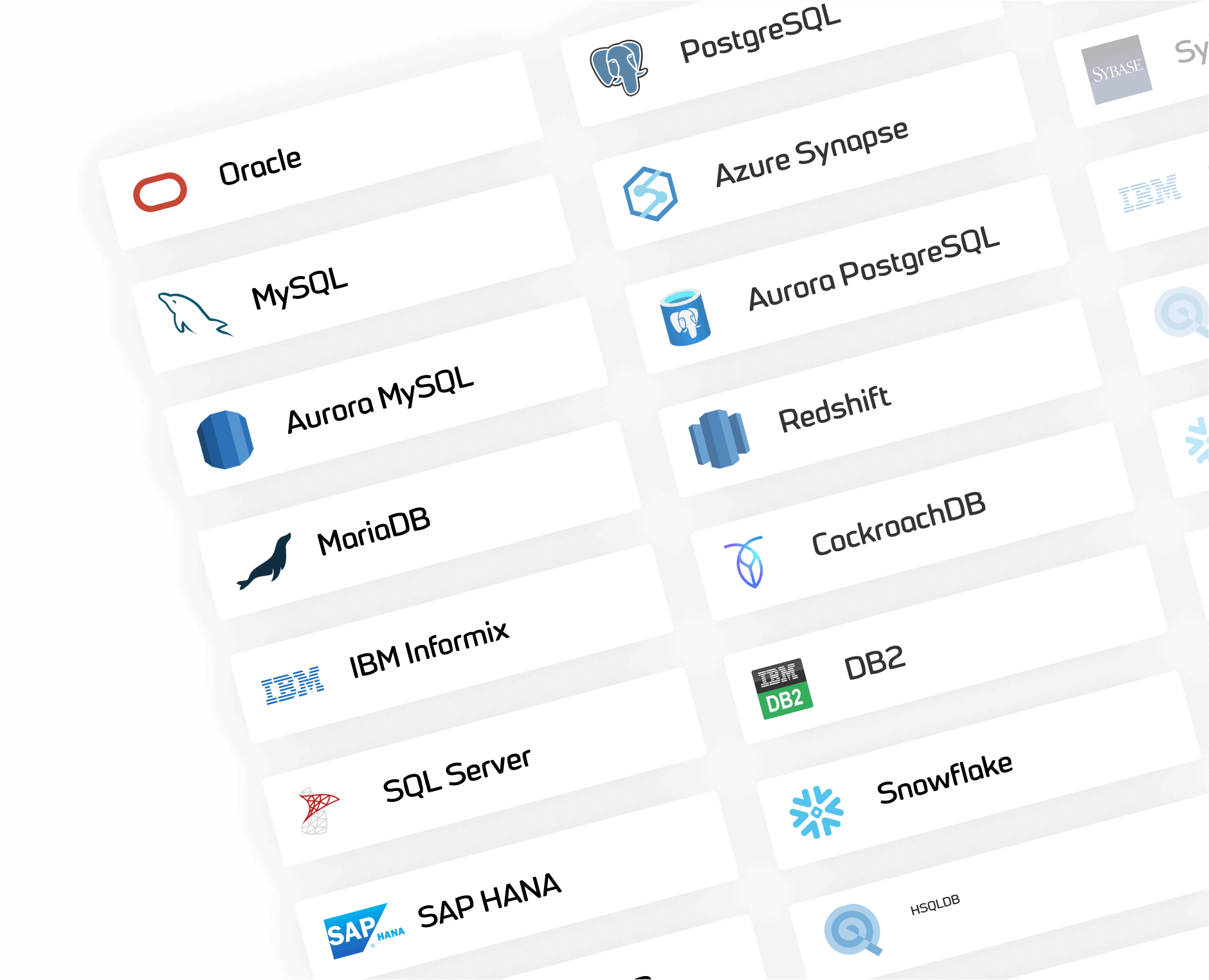
Whether it’s SQL Server, PostgreSQL, Oracle or MySQL, Simple Talk is the one-stop shop for your database of choice – regardless of skill level.
Is your preferred database not listed?
Contact us to let us know what you’d like to see added next.
Connect, learn and grow with Simple Talk
Simple Talk’s commitment to the community extends beyond our vast technical content archive. As a part of Redgate Software, we support conferences and user group events, highlight the community on our podcast, and more.

The Simple Talk podcast
The Simple Talk podcast features hosts Steve Jones, Grant Fritchey and Kellyn Gorman as they discuss technology adoption, career stories, industry challenges and more. From database management and DevOps, to data security and programming techniques, it’s a must-listen for tech industry professionals and enthusiasts.

Contributions from the Redgate Advocates and the Simple Talk community
The blog wouldn’t exist without input from the community – after all, our authors are made up of technology and data professionals from all over the world. Simple Talk aims to provide high-quality, accurate technical content which has been peer-reviewed and written by technology professionals, not AI.

Simple Talk is brought to you by Redgate Software
Redgate creates ingeniously simple software to help organizations and professionals get the most value out of any database, anywhere, through the provision of end-to-end Database DevOps.