This article is part of Aisha Bukar's 6 part series: A Beginners Guide to MySQL Replication. The entries include:
Protecting and controlling access to your data against unauthorized person(s) is crucial in any organization. Unauthorized entry or modification of your data can lead to severe and sometimes irreversible damage.
Just like we mentioned at the beginning of this series, MySQL Replication is a process where data from one MySQL database known as the source is copied over to one or more other databases called replicas. It is possible for data to get breached during this process.
When setting up replication in MySQL, it is essential to understand the security issues that may arise as well as understand ways to counteract them. Choosing the suitable security method for your server instances and setting up ways to recover corrupted or lost information is necessary. In the last part of this series, we will look at security risks, best practices, and backup and disaster recovery methods in MySQL replication.
Importance of Security in Database Systems
Security in database systems cannot be overemphasized especially at a time when careless exposure of data could lead to serious damages. The amount of data stored in databases has significantly increased due to the rapid development of technology around the world, therefore, careful structure needs to be put in place to avoid these data falling into the wrong hands. There are so many factors to consider when looking at security in databases such as data protection, accountability, compliance, and so on. Yet, all of these factors can be distilled into these four essential categories, which are:
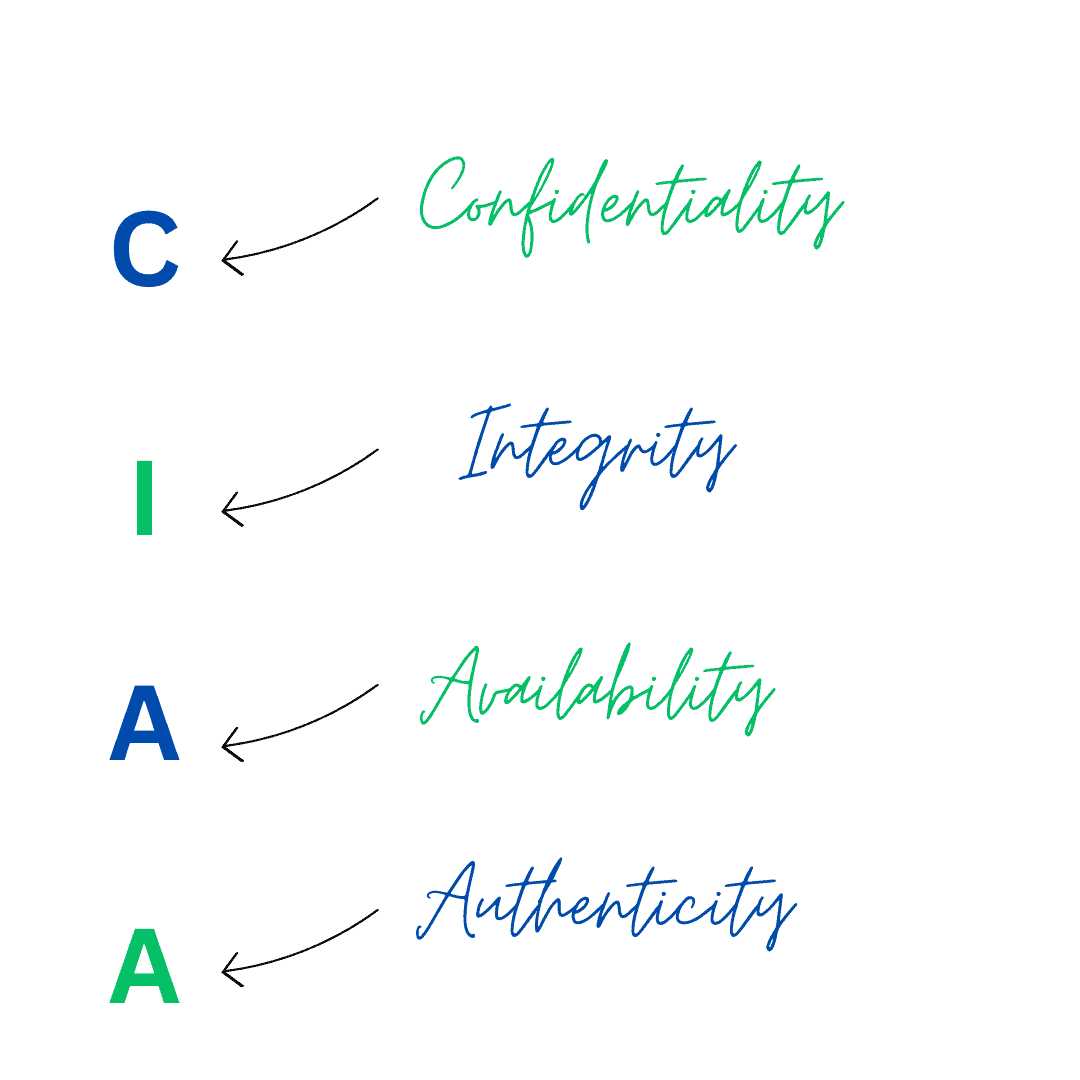
Confidentiality
Keeping your data private and preventing unauthorized access to these data is super important. Data confidentiality aims to protect your data from unwanted access. Neglecting data confidentiality can lead to privacy violations, financial setbacks, legal repercussions, and harm an organization’s reputation. Employing security measures such as access controls, encryption, and login checks helps safeguard confidentiality, they are like your data’s bodyguards.
Integrity
Data integrity is all about ensuring that data remains accurate and reliable from the moment it’s first generated or input into a system, right through its entire life cycle. This is especially crucial in fields like finance, healthcare, and research, where the precision and trustworthiness of data are paramount for making informed decisions and complying with regulations To safeguard data integrity, it’s important to have regular data backups and a robust recovery plan in place. These measures can prove invaluable in restoring data to its accurate and consistent state in the event of data loss or corruption.
Availability
Data availability simply means making sure you can get your data when you want it. Its primary goal is to guarantee that data remains consistently accessible and functional. To maintain data availability, it’s crucial to regularly generate data backups and establish disaster recovery strategies. This is effective in the case of data loss. Also, enforcing strong security measures like firewalls and access control methods helps safeguard data availability and protect against unauthorized entry.
Authenticity
Data authenticity is all about making sure the information in a database is real, correct, and reliable. We need to check that no one has changed it without permission and that it truly shows the right things. Organizations use this data to make big decisions. If the data isn’t authentic, they might make choices that can be harmful. Keeping data authentic is a big part of keeping it safe and making sure it stays authentic.
Security Risks in MySQL Replication
While MySQL Replication is a powerful feature for data transfer and availability, it still introduces different potential security risks that need to be considered and mitigated. Here are some of the security risks you may encounter in MySQL replication:
- Unauthorized access to replication data: When an attacker gains access to a replication stream, they can intercept sensitive data that is being replicated between servers. This sensitive data could be passwords or confidential files or maybe customer data. This could lead to compromising existing data by modification, or sometimes even deletion of the data.
- Authentication and Authorization: If your MySQL credentials are mishandled, it opens the door for attackers to infiltrate your databases, including gaining access to replication privileges. When an attacker gets hold of replication privileges, they can potentially increase their control over the target server, which can result in more serious security breaches. Ultimately, this could lock out authorized users from accessing the database.
- Network Security: If there are no adequate encryption methods in place such as SSL/TLS, the data traveling between MySQL servers during replication becomes vulnerable to interception. This means that if an attacker has access to the network, they can secretly monitor the replication traffic. In the absence of encryption, attackers could even go as far as intercepting (man-in-the-middle attacks) and altering the replication data packets, which can result in data tampering or unauthorized modifications.
- Vulnerabilities in Replication Protocols: Just like any software, MySQL replication itself may be susceptible to some vulnerabilities that attackers can exploit to disrupt the replication process or the entire database system. Regularly updating MySQL and monitoring security performance is essential in addressing these issues.
Best Practices for Securing MySQL Replication
Understanding the potential risks that could occur in a replication topology is one thing, knowing how to counteract these risks is another. There are standard methods available for securing replication, here are some of the best practices:
Implement SSL/TLS encryption
SSL/TLS (Secure Sockets Layer/Transport Layer Security) encryption safeguards the data exchanged between MySQL servers by encrypting it, thus preventing unauthorized monitoring and unauthorized alterations. To use SSL/TLS encryption for replication traffic, you must configure MYSQL replication to use these encrypted connections by taking advantage of OpenSSL. OpenSSL is a freely available software library and set of tools that offers comprehensive support for SSL/TLS protocols, as well as an extensive array of cryptographic features and utilities. Here’s a very basic step on what you need to do:
- Generate a security certificate and the necessary key files using the OpenSSL command line and provide the necessary information.
- Move the certificate and key files to the appropriate location
- Add the certificate and key file-related parameters to the [mysqld] section of the MySQL configuration file (my.cnf or my.ini). Here’s an example of how this may look like:
[mysqld]
ssl-ca=/etc/mysql/ssl/mysql-cert.pem
ssl-cert=/etc/mysql/ssl/mysql-cert.pem
ssl-key=/etc/mysql/ssl/mysql-key.pem Restart the MySQL server to apply the configuration changes.- Create an equivalent certificate from the identical certificate authority generated on the source server for each replica.
- Add the appropriate file parameters to the “CHANGE REPLICATION SOURCE” or “CHANGE MASTER” statement. Here’s an example of how this should look like:
CHANGE MASTER TO
MASTER_HOST='source_server_hostname',
MASTER_USER='replication_user',
MASTER_PASSWORD='replication_password',
MASTER_LOG_FILE='mysql-bin.xxxxxx',
MASTER_LOG_POS=xxx,
MASTER_SSL=1,
MASTER_SSL_CA='/path/to/replica-ca-cert.pem',
MASTER_SSL_CERT='/path/to/replica-cert.pem',
MASTER_SSL_KEY='/path/to/replica-key.pem'; - After configuring the replication source on each replica, start the replication process using the ‘START REPLICA’ or ‘START SLAVE’ command.
This is just a basic guide on how to implement SSL encryption for replication environments. For more information on obtaining an SSL certificate and key files using OpenSSL, please visit the official documentation.
Strong Authentication and Authorization
It is advisable to use complex passwords for your MySQL root accounts. Avoid the use of default usernames or passwords, rather take advantage of password policies that implement different combinations of numbers, letters, and symbols. An important guideline mentioned in the MySQL documentation is also to: “Restrict access to the ‘user’ table in the ‘MySQL’ system database to MySQL root accounts ONLY”. This grants the necessary permissions only to the appropriate users.
Role-Based Access Control (RBAC) can be a valuable approach in MySQL replication. RBAC can improve security by reducing the potential for human error in assigning and managing permissions. It also makes it more difficult for malicious users to gain unauthorized access. Here are some ways to consider implementing RBAC for enhanced security in MySQL replication:
- Clearly define specific replication roles based on the responsibilities and privileges required for replication tasks. For example, you might have roles like “Replication Master,” or “Replication Slave”.
- Determine the specific privileges each replication role should have. For example, a “Replication Master” role might have privileges for creating and modifying replication configurations, while a “Replication Slave” role might have read-only privileges for replication monitoring.
- Users involved in replication should be assigned the relevant replication roles, while users with other database responsibilities should be assigned appropriate database roles.
- Conduct regular reviews of role assignments and privileges to ensure they align with the current requirements and responsibilities of users involved in replication.
- Ensure that each role is assigned the minimum necessary privileges to perform its tasks. This reduces the risk of unintended actions and security breaches.
Implement network security measures
Implementing network security measures is an important aspect of security in MySQL replication. Firewalls are important when it comes to managing incoming and outgoing traffic to and from MySQL servers engaged in replication. Below are key firewall strategies to consider:
- IP Whitelisting: Employ the practice of IP whitelisting to exclusively permit replication traffic from trusted IP addresses or specific subnets. This involves configuring firewall rules that exclusively authorize connections originating from the designated IP addresses of validated MySQL servers, while actively blocking access from all other sources.
- Port Restriction: Limiting the exposure of MySQL replication ports enhances security, typically port 3306 for MySQL. By doing so, you confine access to the MySQL service solely to systems that have been explicitly authorized.
- Logging and Monitoring: Enable the logging and monitoring features of your firewall to actively observe network traffic. This vigilant approach allows for the identification of any unauthorized or suspicious connection attempts, enabling timely detection and response to potential security threats.
It is also advisable to incorporate a Virtual Private Network(VPN). Using a VPN for replication traffic introduces an additional security layer. A VPN typically establishes a secure, encrypted tunnel across the public network, guaranteeing the confidentiality and security of replication data as it traverses the network.
Backup and Disaster Recovery
Preparing for disaster recovery and regularly backing up databases is crucial in case unexpected accidents or disasters occur. MySQL offers replication features such as asynchronous replication, which can be used for disaster recovery. In this setup, the replica server(s) replicates data from the source server. If the source server fails, the replica can take over.
MySQL offers different types of backup methods such as physical backups, logical backups, online backups, offline backups, and snapshot backups, to name a few. It’s important to know some key differences between these backup methods.
For example, logical backups are made using tools like mysqldump to generate SQL files containing both the database schema and its data. Although these files are easy for humans to read, they may perform more slowly for large databases. On the other hand, physical backups entail copying the actual database files, resulting in a faster backup and restore process. However, they may not be as easily transported as logical backups.
Another example would be snapshot backups. Snapshot backups are like quick pictures of your MySQL database that show exactly how it looked at one specific moment in time. For more information on backup and recovery methods, please visit the MySQL official documentation.
Conclusion
At this point, I can safely say it’s crystal clear how security is of paramount importance in MySQL replication. I’d like to express my gratitude for your unwavering support from the start to the very end of this series. I hope you’ve understood how replication works and can put it into practice in real-world scenarios. Thank you for reading!


Load comments