MongoBleed (CVE-2025-14847) was defined as “the vulnerability of the year.” In this article, find out what it is, why it’s dangerous, and if (and when) you should care about it. But first, some context.
Back in April 2014, a vulnerability in the TLS extension ‘Heartbeat’ was discovered by researchers at Google. The vulnerability came about because, at the time, OpenSSL never properly checked the length of any requested data. Attackers could therefore ‘craft’ requests in such a way that harvested personal data. This vulnerability picked up the quite appropriate moniker ‘Heartbleed’.
Heartbleed was dangerous because it focused on leaked memory that could contain highly sensitive information such as private encryption keys, usernames, passwords, and more. It had a huge impact – not only because millions of websites and apps used OpenSSL, but it was also hard to detect since the logs associated with it were well hidden.
So, where does MongoBleed (CVE-2025-14847) come in – and what is it?
Servers running MongoDB using vulnerable OpenSSL versions can leak memory through the Heartbleed bug. Since MongoDB can use OpenSSL for encrypted (TLS) connections, MongoBleed allows attackers to:
- Send a malicious message to keep a TLS session alive (send a TLS „heartbeat“ request.)
- Cause the server to return some of its memory – potentially exposing sensitive information stored or processed by MongoDB.
In theory, attackers could access and extract memory data that might contain private keys, SQL query results stored in memory, or other data. Here‘s a full rundown of how MongoBleed compares to Heartbleed:
| Feature | Heartbleed | MongoBleed |
| Main cause | A bug in OpenSSL | The same bug in OpenSSL |
| Affected applications | Any system running OpenSSL | MongoDB servers running vulnerable OpenSSL versions |
| Discovered on (date) | 2014 | 2025 |
How does MongoBleed work?
To fully understand MongoBleed, it’s first important to know what we‘re talking about in the first place. MongoBleed has a CVE ID of 14847 and affects most versions of MongoDB, including community, enterprise, and MongoDB Atlas. It also affects installations of MongoDB where a server allows for network compression using zlib.
In a nutshell, MongoBleed allows an attacker with an access to a MongoDB instance to extract parts of server memory that may contain sensitive data. To exploit the MongoBleed vulnerability, an attacker should:
- Ensure that MongoDB is reachable over the Internet.
- Ensure that the targeted server has the zlib compression extension enabled (which it is by default.)
What versions of MongoDB are at risk of a MongoBleed attack?
After identifying that the vulnerability could exist, the nefarious party should then ensure that the server is running a vulnerable version of MongoDB. These versions include:
- MongoDB version 3.6
- MongoDB 4.0 and MongoDB 4.2
- MongoDB versions from 4.4.0 to 4.4.29
- MongoDB versions from 5.0.0 to 5.0.31
- MongoDB versions from 6.0.0 to 6.0.26
- MongoDB versions from 7.0.0 to 7.0.26
- MongoDB versions from 8.0.0 to 8.0.16
- MongoDB versions from 8.2.0 to 8.2.2
After identifying that a MongoDB instance is available over the Internet, the server has the zlib compression enabled, and MongoDB is running one of the vulnerable versions, an attacker should exploit the vulnerability and then move on to a different MongoDB instance.
The root cause of this pertains to zlib being enabled on a target server in that:
- MongoDB comes with support for zlib. If it‘s not disabled AND you‘re running a vulnerable version of MongoDB, your data is at stake.
- Messages from the zlib library include length fields.
- The server fails to correctly validate these length fields.
- If an attacker sends malicious length values, the server may:
- allocate a buffer incorrectly or
- return uninitialized heap memory in the response.
Protect your data. Demonstrate compliance.
What does MongoBleed look like?
According to Akamai, the malicious request may look like this:
|
1 2 3 4 5 6 7 8 |
struct OP_COMPRESSED { "uncompressedSize": 99999, "compressedMessage": "<compressed BSON payload that's missing a null terminator>" }; |
What does this mean?
OP_COMPRESSEDis a MongoDB messaging mechanism used when you send compressed data to the server.- We’re telling MongoDB that once the message is decompressed (
uncompressedSize), the result should be 99,999 bytes long (99999). Since we do that, MongoDB will allocate a buffer of 99,999 bytes in size and some of it should remain uninitialized. - We omit the
NULLterminator but ifNULL(\0) is missing, the server may keep reading the memory and search for other data.
In essence, the code tells MongoDB to do the following:
- Allocate a large buffer of 99,999 bytes in size.
- Parse a malformed BSON request.
- Read and/or return data from the memory, thus exploiting MongoBleed.
It’s important to note that such a request doesn’t modify or delete any data. Instead, it reads memory that should never be exposed – hence the purpose of the exploit. An attacker can access a variety of things depending on what data is stored in the operating memory. That’s why CVE-2025-14847 is defined as a “memory disclosure” vulnerability.
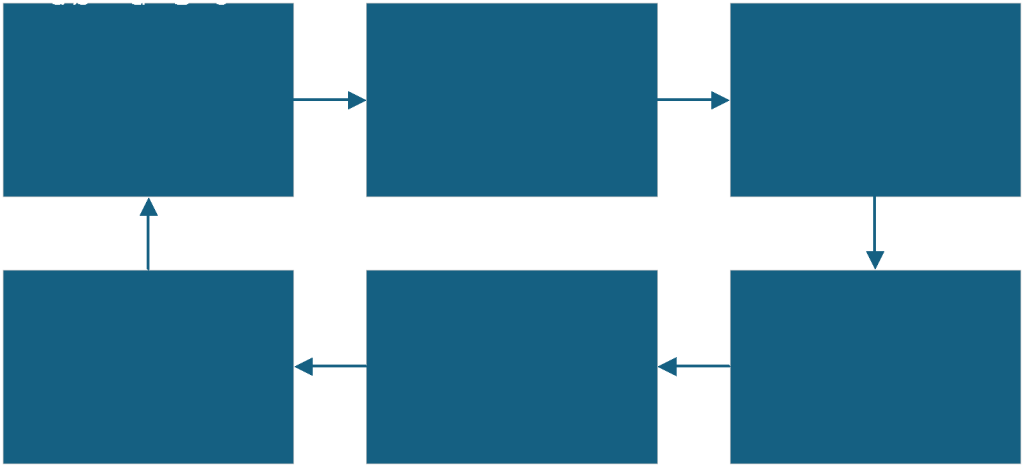
How to prevent the MongoBleed attack
To prevent MongoBleed (CVE-2025-14847) running riot on your MongoDB server(s), making the following logical deductions is enough:
| Feature to exploit the vulnerability | Protection measure |
| MongoDB being available over the Internet. | Don’t expose your MongoDB installation over the Internet. |
| The Linux server having the zlib compression library enabled. | Disable the zlib compression library in php.ini by setting the zlib.output_compression option to Off. |
| The server should run a vulnerable version of MongoDB. | Ensure that your server isn’t running a MongoDB version susceptible to this vulnerability (see above.) |
Put simply: don’t make your MongoDB instances readily available, disable the zlib compression library (if it’s enabled), and/or ensure you’re not running a vulnerable version of MongoDB. Better yet, apply all three measures at once – it’s not hard to do.
Why keeping your software up to date is so important
Last but not least, always keep your software up to date. Remember WannaCry? One of the main reasons why such an attack was so successful was because so many computers disabled, or didn’t update, Windows Update.
Those who did keep their software updated, on the other hand, didn’t feel the effects of the vulnerability. So, always keep your software up to date!
Summary
MongoBleed (CVE-2025-14847) is sort of a ‘play’ on the old Heartbleed flaw, in that both vulnerabilities open up the possibility of inadvertent memory disclosure. And, since they’re both difficult to detect (exploiting such vulnerabilities will not leave any trace in the logs), establishing if you‘re impacted can be quite troublesome.
Ultimately, there are some basic good practices to follow. If you‘re running an updated version of MongoDB, don‘t leave your data widely exposed on the Internet, and turn off the zlib extension in Linux. Plus, for good measure, keep your software up to date!
FAQs: The MongoBleed (CVE-2025-14847) vulnerability in MongoDB
1. What is MongoBleed (CVE-2025-14847)?
MongoBleed (CVE-2025-14847) is a memory disclosure vulnerability affecting certain MongoDB versions when zlib compression is enabled, allowing attackers to retrieve sensitive data from server memory.
2. Why is MongoBleed dangerous?
The vulnerability can expose sensitive information such as encryption keys, credentials, or query results stored in memory without leaving clear traces in server logs.
3. How is MongoBleed related to Heartbleed?
MongoBleed is similar to Heartbleed because both vulnerabilities allow attackers to read server memory due to improper validation of data lengths.
4. Which MongoDB versions are affected by MongoBleed?
Multiple versions of MongoDB are impacted, including releases from the 3.6, 4.x, 5.x, 6.x, 7.x, and early 8.x series when running vulnerable builds.
5. How can you protect your MongoDB server from MongoBleed?
Update MongoDB to a patched version, disable zlib compression if unnecessary, and avoid exposing MongoDB instances directly to the internet.
6. Can MongoBleed modify or delete database data?
No. MongoBleed is a memory disclosure vulnerability that only allows attackers to read data from memory, not alter or delete database records.



Load comments