Active Directory (AD) is one of the most underused technologies from Microsoft. At its core, Active Directory is simply a replicated database. By nature, Active Directory contains computers, users, contacts, groups, any many other objects. Most organizations take AD a bit further by including the DNS role on any domain controller (which in stores DNS information in AD) But Active Directory can do so much more! This can be seen by Microsoft’s recent influx of information into AD such as the storage of BitLocker encryption information and licensing for Windows 8.
Because Active Directory Users and Computer (ADUC) is one of the core tools in any Windows Administrator’s belt, we are going to extend ADUC by automating four common tasks!
Getting Started
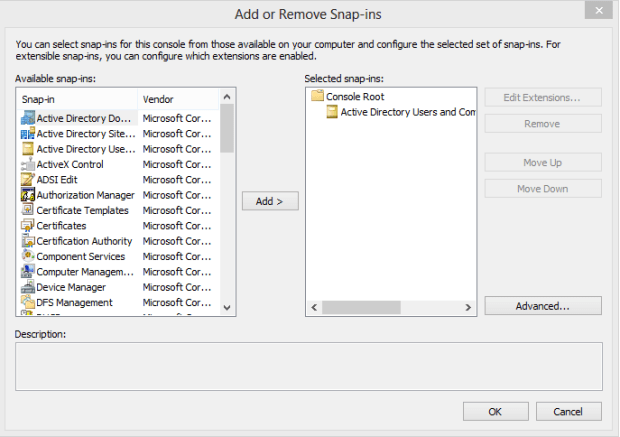
Expanding AD involves the creation of a custom Microsoft Management Console, (MMC) that includes the Active Directory Users and Computers (ADUC) Snap-in. First, fire up MMC.exe. Select ‘File‘ and then ‘Add or Remove Snap-ins‘. Add ‘Active Directory Users and Computers‘ to the list of selected snap-ins.
Because your co-workers will be wanting to get their hands on your MMC, go ahead and save it in a common share.
Task 1: Jumping Around
Regardless of your domain and hierarchy setup, you are likely to have found yourself jumping around between Organization Units (OUs). In our environment, we separate computers and users for each site into separate Organization Units. Because of the number of groups that we have and rights delegation, we further divide our groups into two separate OUs. After all of this, each site has 4 main OUs. With 22 sites, that equates to a lot of jumping around and navigation in ADUC!
Using Favorites will make a world of difference! Make a list of all of your common OUs that you access in a week and group them by function (or what objects they store). In your custom ADUC MMC, select Favorites and then Organize Favorites. Expand the Favorites Folder and create organization folders for each OU group (ex: Computer OUs).
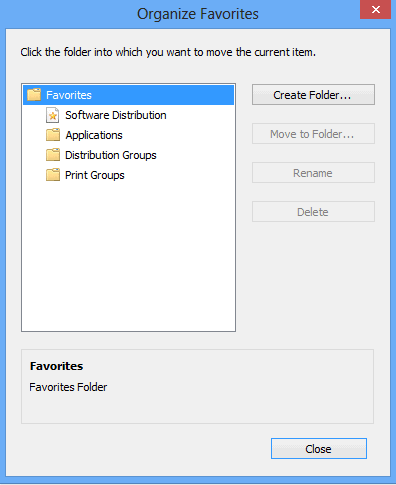
Now, navigate to each OU that you regularly visit. Once there, select ‘Favorites‘, ‘Add to Favorites‘, and then add the OU to the correct folder. After a few minutes, you should have a quick jump list of all common OUs.
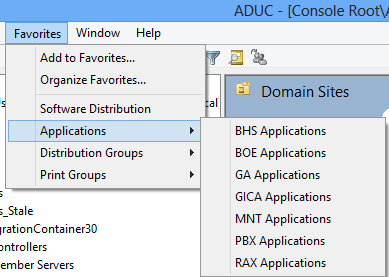
Instead of finding yourself 3 levels deep in an array of OUs, you can quickly jump around your domain structure for your common tasks!
Task 2: Resetting Passwords
A wise man once said, “Show me an IT Pro who cannot script and I will show you one that grinds too many hours”. By bringing in external scripts into your MMC, you’ll find yourself automating problems you never knew existed.
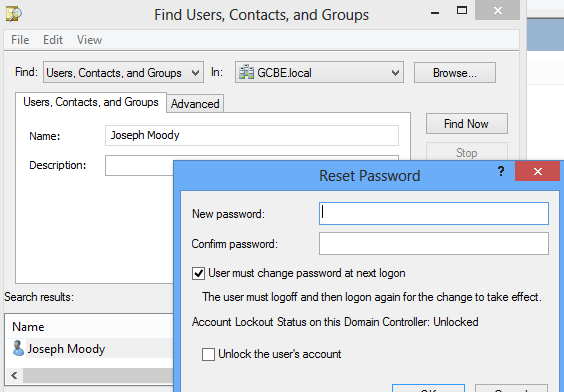
A nearly universal problem in IT is a user forgetting their password. A common response to this problem would be to look up the user in Active Directory and select Reset Password. You would then type in a default password, prompt them to change it on the next logon, and probably unlock their account.
PowerShell can make this process easier by presenting you with relevant information and standardizing on password resets. Let’s take a look at a script that makes use of the Quest AD CMDLETs:
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 |
Add-PSSnapin Quest.ActiveRoles.ADManagement $User=Read-Host "Search for a User by: First, Last, or UserName" if ((get-qaduser $User) -eq $null){ $User=Read-Host "No Users Found. Please specify a valid user" } Get-QADUser $User | Format-Table Name, UserPrincipalName,PasswordAge,PasswordLastSet,PasswordExpires,AccountisLockedOut -AutoSize function isNumeric ($User) { try { 0 + $User | Out-Null return $true } catch { return $false } } if ($user -match "[\d\.]+$"){ Set-QADUser $User -UserPassword defaultpassword -confirm Unlock-QADUser $User } else { $UserPrincipalName= Read-Host "What is the user's Pin number?" Set-QADUser $UserPrincipalName -UserPassword defaultpassword -confirm Unlock-QADUser $UserPrincipalName } pause |
This script starts by prompting for input from you and searches AD for your input. It will then return any user matching your input and generates a table for you containing the Password Age, the last time the password was set, when the password will expire, and the account lock status.
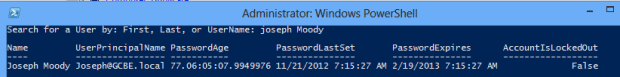
This information allows you to gain a lot of insight into a normal operation. For example, if you see that the password was set on Friday and a user calls on a Monday, you could simply remind the user that they changed their password last week.
Depending on your input, the script may prompt you for the username of the user. Once entered, the script will reset their password to a default value and unlock their user account. This step eliminates confusion between you and the user. If you include personal attributes of your users in AD (such as a date of birth or phone number), you could modify the default password to those attributes. For even the smallest of organizations, this shared information provides additional security.
Task 3: Comparing Group Membership
Managing security groups can be a pain, especially when you start diving into nested groups. If your organization makes heavy use of Group Policy and filtering, you will likely have to compare membership of nested groups. The hard way of doing this is to open both groups up at the same time and recursively go through them. Once you start dealing with overlapping members and multiple layers, this will get old in a hurry.
With PowerShell, this is incredibly easy. Once again, we will make use of the Quest CMDLets. If your organization has at least one Windows Server 2008 R2 domain controller running AD Web Services, you can simulate these same scripts with the Active Directory module.
|
1 2 3 4 5 6 7 8 9 |
Add-PSSnapin Quest.ActiveRoles.ADManagement $Group1=Read-Host "What is the first group?" $Group2=Read-Host "What is the second group?" compare-object -ReferenceObject $(Get-QADGroupMember $Group1 -type computer -Indirect -SizeLimit 6000) -DifferenceObject $(Get-QADGroupMember $Group2 -type computer -Indirect -SizeLimit 6000) -IncludeEqual pause |
This script works by using the Compare-Object CMDLET against two commands that determine group membership. By using the -IncludeEqual option, we will also see a list of computers that are in both groups specified.
Here is how the output looks:
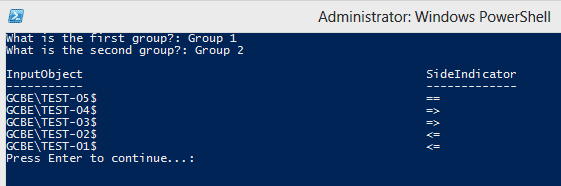
Computers with == sign are in both groups. The <= symbol means the computer is in the first group and the => symbol shows a computer in the second group.
Task 4: Creating Computer Accounts
Each of these tasks so far have dealt with a different area of object management. Now let’s tackle a common complaint with computers, account creation. After your initial domain setup, most organizations will not need to massively create computer accounts. Instead, you might add three to this department or four to a room.
Scripting the addition of a handful of computers could easily take longer than manually creating them. That is not how scripting is supposed to work! Let’s look at a script that will automatically generate computers based on your input instead of a CSV file. Creation this way is much faster!
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 |
Add-PSSnapin Quest.ActiveRoles.ADManagement $SourceComputer = Read-Host "What will be the computer template?" $ParentContainer = (Get-QADComputer $SourceComputer).ParentContainer $Groups = Get-QADComputer $SourceComputer | Get-QADMemberof $prefix = Read-Host "What is the computer prefix? EX: GAMCN or GAMCLABN" try { [int]$startnumber = Read-Host "What number would you like to start with? EX: 01 or 13" -ea "Stop"} catch {"Need to enter a number"; break} try { [int]$number = Read-Host "How many computer accounts do you want to create?" -ea "Stop"} catch {"Need to enter a number"; break} ForEach ($i in ($startnumber..($startnumber + $number -1))) { $compName = $prefix + $i New-QADComputer -name $compName -ParentContainer $ParentContainer foreach ($Group in $Groups) { Add-QADGroupMember $Group $compName} } pause |
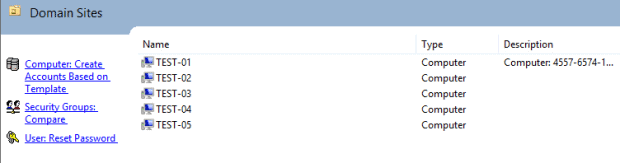
As a practical example, we have an OU with 5 computers in it. We are wanting to add 7 more to it.
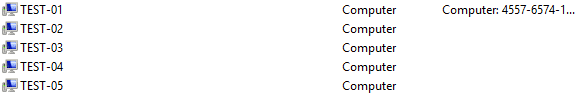
When we run this script, we will be prompted for a template. The new computers created will be based off this template. These computers will be created in the same OU and have the same group memberships as the template computer you specify.
Next, you will be prompted for a naming prefix (ex: Test-) and a starting computer number (ex: 06). Finally, you will be asked how many computer accounts need to be created (ex: 7). This script will dynamically create the new computers faster and more accurately than you could do yourself!
Adding our Tasks to AD
Our last step is to add each of these scripts into our custom MMC. Embedding each of these tasks into AD involves creating a Taskpad view. To do this, select any OU. Then go to Actions and New Taskpad view. Name your view and select your style. Personally, I prefer the vertical list.
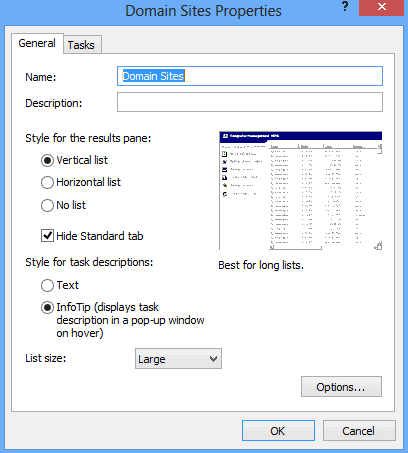
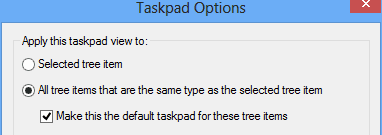
Now select options and ensure that “All tree items that are the same type…” is marked and the checkbox is enabled.
Press ‘OK‘ and navigate to the Tasks window. Select ‘New‘ and ‘Shell Command‘. For the command, enter c:\windows\System32\WindowsPowerShell\v1.0\powershell.exe. For your parameters, enter –command “”&” ‘”PATHTOSCRIPT””.
Next, name your task. For organization, I like to prefix my tasks with their function. This allows for me to quickly find the specific task I want.
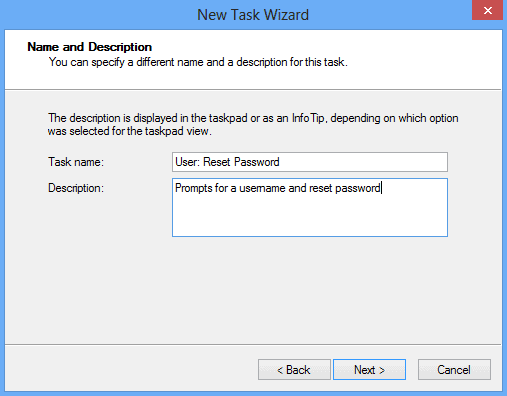
Finally, pick your task icon and press ‘Next‘. Check the “When I click finish” box and repeat until all of your tasks have been created.
You now have an extended Active Directory Users and Computers MMC customized for your common tasks. Through these customizations, you have: created Favorites, automated computer account creation, analyzed group membership, and made resetting passwords a piece of cake!

Load comments