Docker is an open-source platform that enables developers to automate the deployment and management of applications using containerization. It was created by Solomon Hykes and his team at Docker, Inc., and was first released in 2013. Docker allows developers to package their applications and their dependencies into lightweight, portable containers that can run consistently across different computing environments. Docker introduced a new level of efficiency in application deployment by leveraging containerization technology.
Containers provide an isolated and consistent runtime environment for applications, ensuring they run the same way across different infrastructure setups; this enables easy portability and eliminates many compatibility issues. Docker’s containerization model aligns well with the DevOps philosophy and practices; it simplifies the process of building, testing, and deploying applications, making adopting continuous integration and continuous deployment (CI/CD) workflows easier.
Docker allows developers and operations teams to work seamlessly, promoting collaboration and faster release cycles. Docker enables horizontal scalability, allowing applications to be easily replicated and distributed across multiple containers and hosts; scalability, combined with Docker’s lightweight architecture, results in efficient resource utilization.
Docker containers share the host operating system’s kernel, reducing overhead and improving performance. Docker provides application isolation, ensuring that each container operates independently of others on the same host; isolation enhances security by preventing applications from interfering with each other or accessing unauthorized resources. Docker offers features like image signing and vulnerability scanning to enhance container security.
Docker Hub, the official public registry for Docker images, became a central repository for sharing and discovering containerized applications and services; it facilitated the creation of a vast ecosystem of pre-built images that developers could leverage, accelerating Docker’s adoption and ease of use. Docker quickly gained widespread popularity and attracted a large and vibrant community of developers, operators, and organizations; this community actively contributed to the improvement of Docker through the creation of tools, libraries, and best practices.
Overall, Docker revolutionized how applications are packaged, deployed, and managed, leading to its rapid popularity. Its ease of use, portability, scalability, and efficiency have made it a fundamental tool in modern software development and deployment workflows.
Docker Security Principles:
Docker incorporates several inherent security features that contribute to its overall security posture. When you use Docker to quickly create an environment and test some code, security is important enough (especially if you execute any , but when using Docker for production, multi-user environments, it is essential to treat the container as you would any other server environment.
The following is a list of some of the basic security principles that are baked into Docker.
- Container Isolation: Docker containers provide isolation, allowing applications to run independently of each other and the underlying host system; this isolation prevents applications from interfering with one another and helps contain the impact of security breaches.
- Resource Limitations: Docker allows resource limitations for containers, such as CPU and memory usage restrictions; this feature prevents containers from monopolizing system resources and helps mitigate denial-of-service attacks or resource exhaustion vulnerabilities.
- Image Signing and Verification: Docker supports image signing, allowing developers to sign container images to ensure their integrity and authenticity, image verification mechanisms verify the signatures to ensure that only trusted and validated images are used, reducing the risk of tampering or unauthorized modifications.
- User and Access Management: Docker enables fine-grained control over user permissions within containers; it allows users to run containers with limited privileges, reducing the attack surface and potential impact of security breaches. Docker also supports integration with external authentication and authorization systems, facilitating centralized access control management.
- Networking and Firewalling: Docker provides container network isolation, enabling fine-grained control over inbound and outbound network connections; administrators can configure network policies, restrict container network access, and implement firewall rules to control traffic flow and protect against unauthorized access.
- Logging and Auditing: Docker captures container logs, including standard output and error streams; these logs can be collected and monitored centrally, aiding in security incident detection, investigation, and compliance auditing.
Understanding Docker Security Limitation:
The question of how to enhance container security is unavoidable given the increasing popularity of container-based applications; before planning containerization, businesses need to understand the security limitations and plan mitigation to protect their infrastructure. Below are some of the main limitations companies should consider,
- Shared Kernel: Docker containers share the host operating system’s kernel, meaning a kernel vulnerability can affect multiple containers. While container isolation prevents direct kernel access, it does not eliminate the risk; regularly updating the host kernel and monitoring security advisories are essential to mitigate this risk.
- Vulnerabilities in Images: Docker images can contain vulnerabilities in their underlying software packages; it is crucial to regularly scan and update container images to patch known vulnerabilities and ensure that only secure images are used in production.
- Container Breakouts: Although container isolation is designed to prevent containers from escaping their boundaries, specific vulnerabilities or misconfigurations may still allow container breakouts; it is vital to apply proper security measures, such as using secure images, configuring container runtime restrictions, and regularly updating Docker versions to mitigate these risks.
- Securing the Host: Since Docker containers rely on the underlying host system, securing the host is critical; any compromise of the host system can potentially impact the security of running containers, employing host-level security measures, such as regular patching, securing access to the host, and implementing intrusion detection systems, is crucial.
- Orchestration and Management: Docker’s inherent security features focus on container runtime and isolation; however, additional security considerations arise when deploying Docker containers at scale using orchestration frameworks like Kubernetes. Properly configuring and securing the orchestration platform, managing secrets and credentials, and applying network security measures become critical in such environments.
To maximize the security of Docker deployments, organizations should combine the inherent security features of Docker with best practices like regular patching, vulnerability scanning, secure image management, access control, monitoring, and ongoing security education and awareness for developers and administrators. Additionally, adopting a defense-in-depth approach that includes multiple layers of security controls helps mitigate the limitations and enhances the overall security of Docker-based environments.
Docker Container Attacks Models and Mitigation:
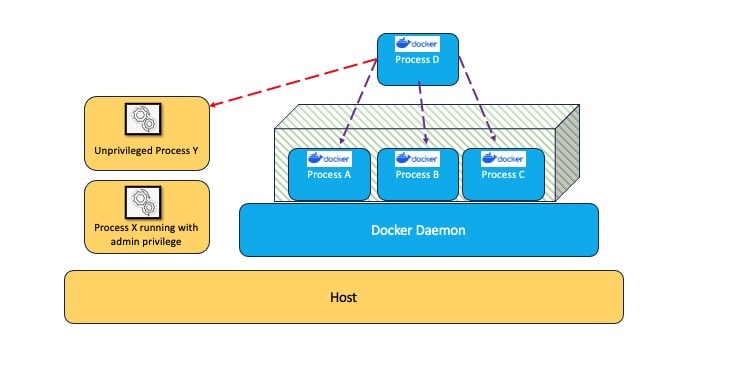
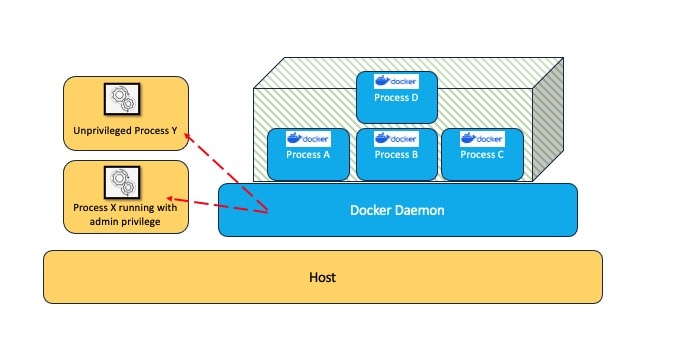
The container attack model has two perspectives: inside and outside a container. We see the container-like process running inside the container, which is isolated from the host and can execute commands inside containers. When we think of an outside container, the user can see the docker daemon process and all its child processes and execute commands directly on the host. Users can execute commands directly on the host if they have permission to use Docker. An attacker model represents how a malicious actor would attack a system considering the above perspectives.
Inside a Container
Let’s consider a scenario where a malicious actor has access to a container where they can execute commands and have everything inside a container but cannot access other containers or the host. In this scenario, an attacker’s primary Goal is to escape a container’s isolation, referred to as Container Escape.
As shown in the following image, once container escape is successful, Process D can access another container process: A, B, and C; containers are not only isolated from the host, but they should not access another container. Another vector we see here is Process D accessing Process Y, which is running on the host and also able to read and write files on other containers, namely A, B, and C. Imagine a situation: a PaaS offering company that offers small businesses to run their Docker containers; a malicious attacker could have a docker image running an adversarial process that escapes a container and tries to access underlying infrastructure or other containers running on the same platform. It will be a sensitive data exposure and compliance issue for the PaaS offering organization.
Most of the time, the System Administrator follows the common practice of connecting the sockets as volumes to provide containers with API access; this allows containers to monitor and analyze other containers. If the Administrator mounts /var/run/docker.sock to a container, it can access the API even if it’s mounted as a read-only volume. This configuration allows the container full access to docker on the host. An attacker can use this misconfiguration to escape isolation and create another container with arbitrary volumes and commands. It is even possible to remote shell on other containers. Follow the below example of leaking Postgres password information,
Postgres database is started with providing a password in a POSTGRES_PASSWORD environment variable. If the attacker has access to another container with access to Docker API, he can read the Postgres password.
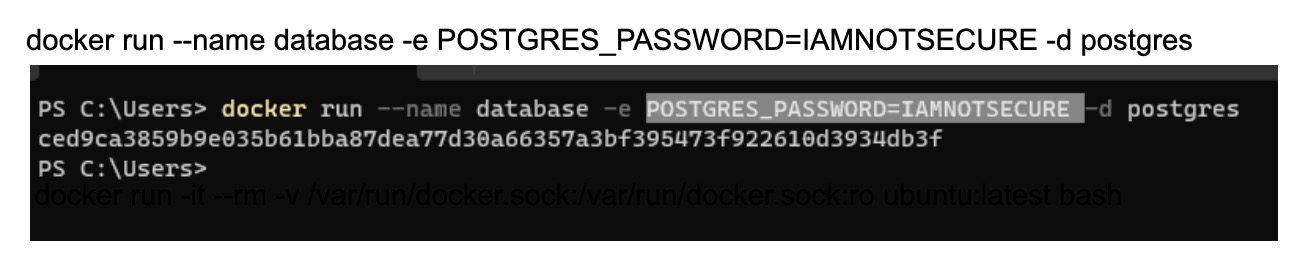
Postgres database started with plain text password.
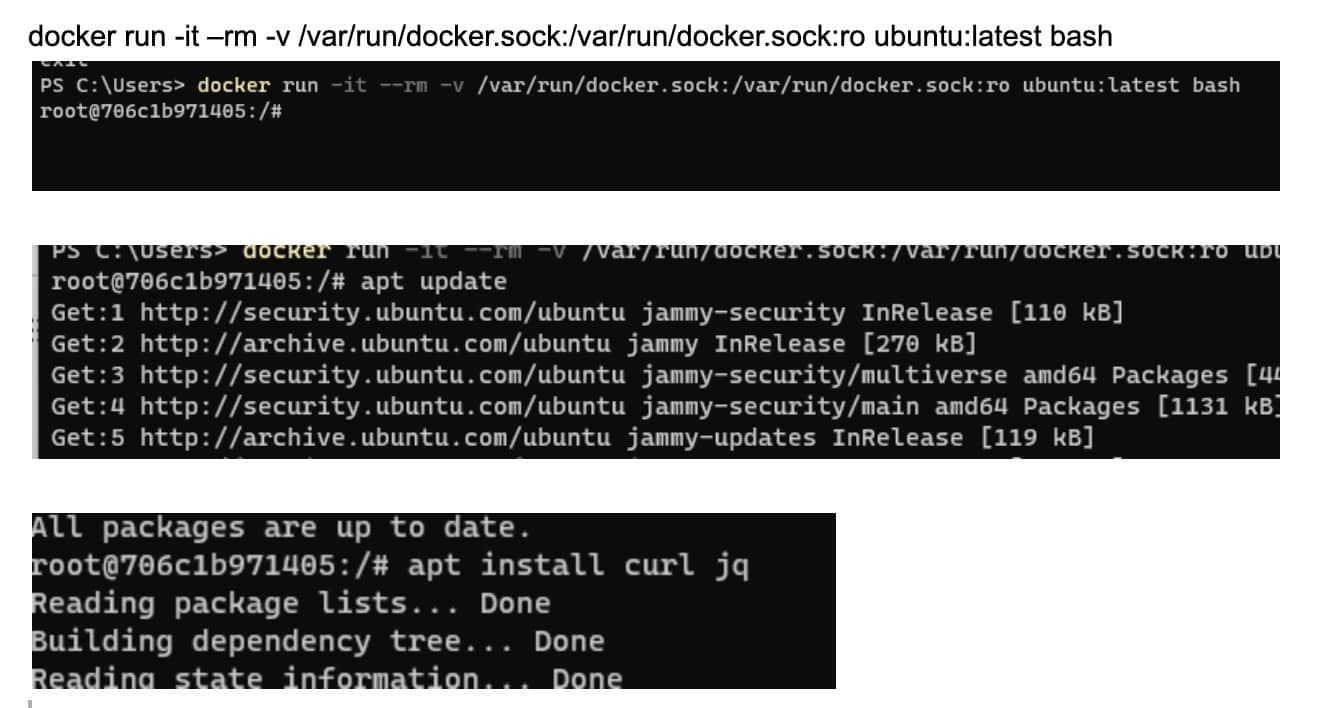
Running docker ubuntu image.
Postgres password exposed “IAMNOTSECURE”
Outside a Container
Another scenario where the user has unprivileged access to the Docker-installed host. Sometimes referred to as Container Breakout, this is where a user that should be limited to only container access, but they instead they can access resources outside the container.
Users can read configuration files or access sensitive information by interacting with Docker Daemon. The Goal for an attacker here is to perform malicious actions via Docker Daemon, referred to as Docker Daemon Attacks. Malicious actors attempt to exploit vulnerabilities in the Docker Daemon, a critical component of the Docker containerization platform.
Docker Daemon, or dockerd, manages Docker containers on a host system. When Docker Daemon is compromised, it can lead to various security risks and potentially allow attackers to gain unauthorized access or control over the host system and its containers.
Docker Daemon Attack
Mitigation for container breakout includes enforcing proper container isolation, implement strong access controls, and regularly update the host system and container runtimes.
Privilege Escalation
In the privilege escalation attack model, attackers aim to escalate their privileges within a container or on the host system to gain full control of the system; this can be achieved by exploiting misconfigurations, insecure container settings, or kernel vulnerabilities.
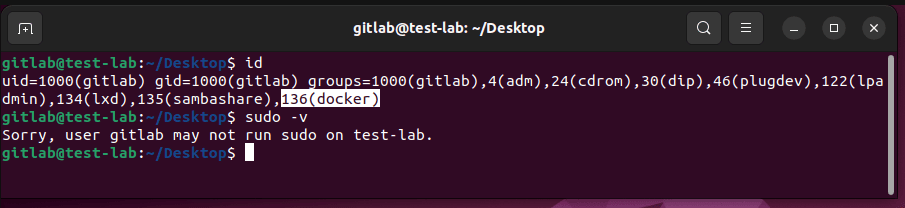
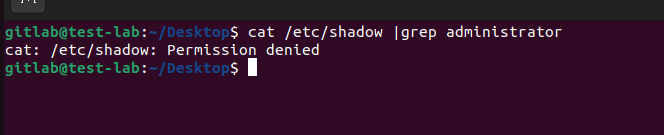
The following image shows that an unprivileged gitlab user belonging to the docker group cant access the/etc/shadow file to get the Administrator hash; he can obtain those running containers in Fig 1.8
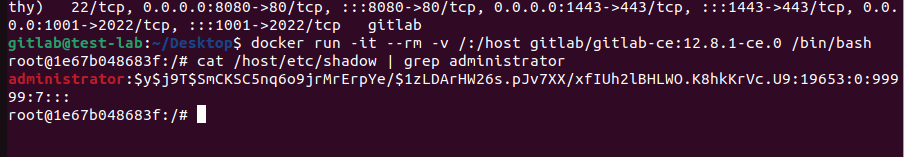
Unprivileged gitlab user can access Administrator hash via running container.
Mitigations include apply the principle of least privilege by configuring containers with minimal privileges, restricting access to sensitive resources, and regularly patching the host system and container runtimes.
Other representative attack types
There are plenty of other attack types that you always need to be aware of when you are using Docker with any kinds of
- Container Image Vulnerabilities –Attackers exploit vulnerabilities within container images, such as insecure dependencies or misconfigurations; by leveraging known vulnerabilities, attackers can gain control over the container or launch attacks on other systems.
Mitigation: Regularly scan container images for vulnerabilities, use trusted base images, keep images and dependencies up to date, and implement secure image registry practices.
- Container Network Attacks – Adversaries target container networks to intercept or manipulate traffic, launch network-based attacks, or gain unauthorized access to sensitive data; techniques include network sniffing, Man-in-the-Middle (MitM) attacks, and exploiting network misconfigurations.
Mitigation: Implement network segmentation, encrypt container traffic, use secure network protocols, and enforce strict access controls on container networks.
- Supply Chain Attacks – Adversaries compromise the software supply chain to introduce malicious or vulnerable components into Docker images or repositories; compromised or malicious images can lead to security breaches or malware distribution within containerized environments.
Mitigation: Use trusted sources for Docker images, employ image signing and verification, regularly scan images for vulnerabilities, and ensure secure image distribution and registry practices.
- Insider Threats – Insiders with authorized access, such as developers or administrators, may intentionally or inadvertently misuse their privileges to compromise container security; insider threats can lead to unauthorized access, data leakage, or intentional sabotage.
Mitigation: Implement proper access controls and least privilege principles, monitor user activities, enforce separation of duties, and educate personnel on security best practices.
By considering all the attack models listed, organizations can implement appropriate security measures to mitigate risks and enhance the security of their Docker containers and environments. Adopting a multi-layered security approach encompassing secure configurations, regular updates, monitoring, and incident response capabilities is crucial.
Testing Docker System for vulnerabilities:
When testing a Docker system for vulnerabilities, it’s essential to follow a structured approach to ensure comprehensive coverage and accurate results. In this section I will summarize some of the methodologies for testing Docker systems for vulnerabilities:
Information Gathering:
- Obtain information about the Docker environment, including the version of Docker, the operating system, network configuration, and any exposed services.
- Identify the Docker images, containers, and associated technologies in use.
Vulnerability Scanning:
- Conduct vulnerability scanning on Docker images and related components. Use specialized container security tools to identify known vulnerabilities within the images.
- Perform vulnerability scanning on the underlying host system to identify any security weaknesses that could impact Docker security.
Configuration Review:
- Review the configuration settings of Docker, including the Docker daemon and its associated files.
- Check for misconfigurations, insecure defaults, or weak security settings that could expose the Docker system to vulnerabilities.
Container Breakout Testing:
- Assess the effectiveness of container isolation by attempting container escapes and privilege escalation.
- Exploit misconfigurations, kernel vulnerabilities, or container escape techniques to gain unauthorized access to the underlying host system.
Network Security Testing:
- Evaluate the network security of the Docker system—test for potential misconfigurations, insecure network protocols, or exposed ports that could be exploited.
- Test for common network-related vulnerabilities like man-in-the-middle attacks, spoofing, or weak encryption.
API and Service Testing:
- Assess the security of Docker APIs and any exposed services used for container orchestration or management.
- Test for API vulnerabilities, such as insecure authentication, authorization issues, or injection attacks.
Privilege Escalation and Access Control Testing:
- Evaluate the effectiveness of access controls and privilege management within the Docker system.
- Attempt to escalate privileges within containers, gain unauthorized access to resources, or bypass access controls.
Data Management and Storage Testing:
- Assess the security of data management and storage within Docker containers.
- Test for vulnerabilities in container volume configurations, persistence mechanisms, or insecure storage access controls.
Logging and Monitoring:
- Review the logging and monitoring practices of the Docker system.
- Check if logs are correctly collected, monitored, and retained for effective incident response and forensic analysis.
Reporting:
- Document all identified vulnerabilities, their severity, and their potential impact.
- Provide clear recommendations for remediation, including patches, configuration changes, or security best practices.
- Include a detailed report with findings, supporting evidence, and steps to address identified vulnerabilities.
Always obtain proper authorization before conducting any testing activities and adhere to legal and ethical guidelines. Communicate and coordinate with the stakeholders to minimize any potential impact on the production systems.
Top 5 Docker Security Vulnerabilities:
The following are the top 5 Docker security vulnerabilities as of this writing. Just like most software, there are virtually always vulnerabilities that you need to be aware of that are similar to the following.
- CVE-2019-15752: Docker Desktop Community Edition before 2.1.0.1 allows unprivileged users to escalate privilege by placing a Trojan horse docker-credential-wincred.exe file in %PROGRAMDATA%\DockerDesktop\version-bin\ as a low-privilege user and then waiting for an admin or service user to authenticate with Docker, restart Docker, or run ‘docker login’ to force the command.
- CVE-2019-14271: The Docker copy (docker cp) command, used to copy files between containers, has a significant code injection problem. An attacker who exploits this weakness can escape the container completely.
- CVE-2019-5736: A weakness in how runc handled system file descriptors was discovered when executing containers. A hostile container might exploit this weakness to overwrite the runc binary’s contents and execute arbitrary instructions on the container host system.
- CVE-2014-9357: A problem in the way the Docker service unpacked images or builds after a “docker pull” was discovered. An attacker might exploit this weakness to distribute a malicious image or build that, when unpacked, would provide them elevated access to the machine.
- CVE-2014-0048: A problem was discovered in Docker prior to 1.6.0; some Docker programs and scripts are downloaded via HTTP and then executed or used in dangerous ways.
Conclusion:
Docker security is a critical consideration for organizations deploying containerized applications. Docker provides various built-in security features, but it’s important to implement additional measures and best practices to ensure a robust and secure Docker environment.
By following industry best practices and adopting a multi-layered security approach, organizations can significantly enhance the security of their Docker environments, protect their applications and data, and minimize the risk of security breaches or compromises. It’s essential to regularly review and update security practices as new threats emerge and Docker evolves.
Of course, no matter how well you think you are protected from vulnerabilities, you still need to stay informed about the latest security updates, vulnerabilities, and best practices to ensure ongoing protection of your Docker systems.

Load comments