Exchange Server has supported the use of rights management since the first days of Exchange Server 2003. Even so, the Exchange Server 2003 implementation tended to be a bit annoying for users. When users attempted to open messages subject to rights management, they were prompted to enter their authentication credentials every time, prior to being able to view the message. As you can imagine, this seriously reduces efficiency if a user needs to open a significant number of rights managed messages.
Fortunately, things have improved in Exchange Server 2007. Users who are running at least Microsoft Office Outlook 2007 or Windows Mobile 6.0 now have the ability to open rights managed messages without being prompted to enter their credentials. In this article, I will explain why this is possible, and how to configure rights management in an Exchange Server 2007 environment.
The Rights Management Server
As mentioned before, rights management has been available for quite some time. Prior to the release of Windows Server 2008, Microsoft’s rights management solution was a product named Rights Management Services (RMS). Aside from the Exchange Server issues that I mentioned earlier, Rights Management Services was a good product. The only problem was that it came with a price tag that put it out of reach for many small and medium-sized companies.
Since the time that rights management was first introduced, there have been several new federal regulations introduced that affect the way that certain types of data must be handled. Since many of these regulations provide stiff penalties for the mishandling or accidental disclosure of data, Microsoft decided to incorporate Right Management Services directly into Windows Server 2008, rather than requiring customers to buy an entirely separate product. Before you get too excited though, keep in mind that there is a Client Access License requirement associated with using Rights Management Services.
New Rights Management Features
Obviously the greatest change in Rights Management Services is that it is no longer a separate product from Windows Server. Aside from this, there have been a substantial number of other changes that you need to be aware of.
One very welcome change is the new self enrollment feature. The previous version of Rights Management Services required administrators to connect to a special Microsoft enrollment server via the Internet. The enrollment server would issue a Server Licensor Certificate (better known as a SLC). The SLC gave the server the right to issue licenses.
The new self enrollment feature does away with this requirement. Windows Server 2008 uses the self-enrollment certificate to sign the SLC without the aid of an external certificate Authority.
Another change to Rights Management Services is that it now supports the delegation of roles. You can use these roles to provide IT staff with varying degrees of administrative control over the Rights Management Server. The table below lists the roles that are available for use:
|
Role Name |
Function |
|
AD RMS Service Group |
The AD RMS Services Group is simply a group that contains the AD RMS service account. When you install the Rights Management Service, the service account that you specify during the installation process is automatically added to this group. |
|
AD RMS Enterprise Administrator |
As the name implies, AD RMS Enterprise Administrators have all of the necessary rights to manage rights management related policies and settings. |
|
AD RMS Template Administrator |
AD RMS Template Administrators have permission to create new rights management templates, or to modify existing templates. They do not have the rights to modify non template related server settings. |
|
AD RMS Auditor |
The AD RMS Auditor role is a role that Microsoft created in order to help organizations to comply with various federal regulations. It is a read only administrative role that allows an auditor to view rights management logs and create reports. |
The other new Rights Management Services feature is its integration with the Active Directory Federation Service (ADFS). ADFS is beyond the scope of this article, but I wanted to at least mention it.
Rights Management Functions
A Windows Server 2008 Rights Management Server provides three primary functions. Exchange Server 2007 is a rights managed application, which means that it utilizes these three primary functions, but also builds on them.
The first and most obvious function of RMS is that it allows authorized users to create rights managed files and templates. In order to perform this function, the application that is used to produce the rights protected document that is to be rights protected must also support rights management. Fortunately, all of the Office 2007 applications (including Outlook 2007) support rights management.
This might be a good time to point out that rights management is different from Digital Rights Management (DRM). Rights management, as I am referring to it, is a mechanism for encrypting documents (or in this case, e-mail messages), and assigning permissions to control who can do what with the protected document. DRM, on the other hand, is basically a copy protection mechanism that is used mostly by content providers. For example, many Web sites that offer online video use DRM to prevent subscribers from downloading all of the site’s content, and then canceling their subscriptions.
The second primary function of the Rights Management Server is its ability to identify trusted users and groups. The Rights Management Server accomplishes this task by issuing a rights account certificate to the users and groups who have been granted permission to create rights protected content.
The third primary function of the Rights Management Server involves allowing the use of protected content. If a user wants to open a protected document, they must possess the proper rights account certificate. Beyond that, the Rights Management Server must cross reference the user or group with Active Directory in order to determine whether or not they have the rights to decrypt the protected document, and what the document’s policies allow them to do with the document (modify, copy, print, etc.).
Rights Management Services and Exchange Server 2007
As I mentioned earlier, Exchange Server 2003 worked with RMS, but it was a pain to use. When Outlook users opened a protected message, they were prompted to enter their credentials, even though they had already been authenticated by Active Directory during their initial login. Typically, Windows Mobile users were completely unable to open rights managed E-mail messages, because they could not connect to Rights Management Services.
Rights Management Service support works a bit differently in Exchange Server 2007 than it did in Exchange Server 2003. When you install the Hub Transport role on an Exchange 2007 server, the installation process automatically installs a component called the AD RMS Prelicensing Agent. The basic idea behind this component is that it certifies the identity of Outlook 2007 and Windows Mobile 6.x users at the Hub Transport level. That way, Exchange is able to perform the various rights management related tasks before the user attempts to open a protected message. This means that Outlook no longer needs to prompt users for their credentials every time that they attempt to open a rights managed message. This new architecture also means that it is even possible for users to open RMS protected messages when they are working offline, something business travelers are sure to appreciate.
Some Caveats to Be Aware of
Although Exchange Server 2007 automatically installs the Prelicensing Agent on any Hub Transport servers, there are a few gotchas that you need to be aware of. For starters, the Prelicensing Agent is only included in Exchange Server 2007 SP1. Therefore, if you are installing the RTM version of Exchange Server 2007 onto a Hub Transport server, the Prelicensing Agent will not be installed.
Another caveat that you need to be aware of is that the Prelicensing Agent does not work with older versions of Rights Management Services. If you’ve got a legacy RMS Server in place, you can use it, but you will have to install SP2 for Rights Management Services 1.0. Of course, if you are using the Windows Server 2008 version of RMS (often referred to as AD RMS or AD RMS 2008), then you are good to go.
An additional requirement that you must be aware of is that if your organization has multiple Hub Transport servers, then each of those Hub Transport servers must be running Exchange Server 2007 SP1 or higher. The reason for this is that the Prelicensing Agent works at the Hub Transport server level. If multiple Hub Transport servers exist, then any one of them could potentially be called upon to deliver a protected message, and must therefore contain the Prelicensing Agent, which of course is only available in SP1.
Preparing to Use the Prelicensing Agent
So far I have talked about some prerequisites for installing the Prelicensing Agent, but there are a couple more requirements that must be met before your organization can use the Prelicensing Agent. The first of these requirements is that there is a client component that must be installed on your Hub Transport servers. The client component that you must use depends on the version of Windows Server that the Hub Transport server is running on.
If your Hub Transport server is running Windows Server 2003, then you will have to install the Windows RMS Client 1.0 SP2. This client will only run on 64-bit versions of Windows Server 2003 (and Windows XP). That shouldn’t be a problem though, since you should never run the 32-bit version of Exchange Server 2007 in a production environment. You can download the client component at: Microsoft Windows Rights Management Services Client with Service Pack 2 – X64 Edition
If you are running your Hub Transport server on Windows Server 2008, then the server must be running the Active Directory Rights Management Client. Fortunately, this client component is installed by default on 64-bit versions of Windows Server 2008.
The other thing that you will have to do prior to using the Prelicensing Agent is to enable it. Although Exchange Server 2007 SP1 installs the Prelicensing Agent by default, it does not enable the agent by default. Thankfully, the technique for enabling the Prelicensing Agent is fairly simple. In order to enable the Prelicensing Agent though, you will have to log into the Hub Transport server using a domain account that is both a member of the Exchange Organization Administrators group and a member of the local Administrators group for the Hub Transport server.
Once you have logged in, open the Exchange Management Shell. I recommend getting started by verifying the Prelicensing Agent’s status. You can do so by entering the following command as shown in Figure A:
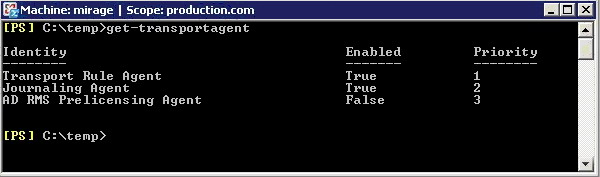
Figure A: Executing Get-TransportAgent
|
1 |
Get-TransportAgent |
Keep in mind that this command may also report the status of some unrelated transport agents, such as the Transport Rule Agent or the Journaling Agent.
Now that you have verified the Prelicensing Agent’s status, you can enable it. Once again, you will perform this task through the Exchange Management Shell. The process involves enabling the Prelicensing Agent, and then stopping and then restarting the Exchange Transport Agent. After the Exchange Transport Agent starts back up, I recommend checking the Prelicensing Agent’s status one more time, just to make sure that it is enabled. This entire process can be completed by entering the following four commands:
|
1 2 3 4 |
Enable-TransportAgent "AD RMS Prelicensing Agent" Net Stop MSExchangeTransport Net Start MSExchangeTransport Get-TransportAgent |
Using Microsoft Outlook with Rights Management Services
Both Outlook 2003 and Outlook 2007 can use rights management, but for the purposes of this article, I am going to limit my discussion to talking about Outlook 2007. Having said that, there are two different ways in which your end users can use Outlook to send rights managed messages. One method involves using your Rights Management Server, and the other involves using a Rights Management Server that is provided by Microsoft.
This can actually be a bit confusing for users, because Outlook is designed to use Microsoft’s Rights Management Server by default. To see what I am talking about, open Outlook 2007, and compose a new message. Now, click on the Microsoft Office button (sometimes called the orb or the Jewel) that is located in the upper left corner of the New Message window. Next, choose the Permissions command from the resulting window. When you do, you will be given the option of assigning the Do Not Forward attribute to the message that you are composing, or of managing the message’s credentials. If you select either of these options though, then you will be prompted to sign up for Microsoft’s free Rights Management Service, as shown in Figure B.
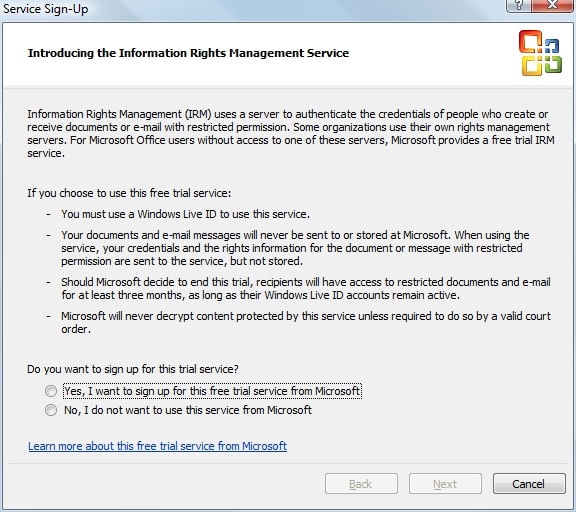
Figure B: sign up screen for Rights Management Service,
Of course this raises an interesting question. Why should you bother with the hassle of setting up your own Rights Management Server if Microsoft offers one that you can use for free? Well, there are a couple of reasons why it is better to have your own Rights Management Server.
For starters, if you read the text on the dialog box that I talked about earlier, it indicates that this is a “trial” service that Microsoft may choose to discontinue at any time. Granted, this trial service has been available for at least a couple of years now (I can’t recall exactly when Microsoft first started offering it), but you never know when Microsoft may choose to end the trial program.
Microsoft has indicated that if they decide to discontinue the trial program, then users will continue to have access to rights managed documents for three months after the program ends. From a business prospective, it is simply a bad idea to encrypt e-mail messages using a service that may be discontinued at the drop of a hat. This is especially true since business needs or federal regulations often mandate the long term storage of e-mail messages. If a message is important enough to protect with RMS, then there is a good chance that it may also be important enough to hang on to for an extended period of time.
If you are still thinking of using Microsoft’s free RMS service, remember that they have only committed to making documents accessible for three months after the service ends. They have not committed to notifying you that the service is no longer being offered. In all likelihood, Microsoft will probably notify their customers, if or when the free RMS service is ended, but you just never know whether or not your spam filter could snag the notification. Microsoft probably isn’t going to wait around for you to confirm that you have received notification of the service’s termination. More than likely, you would simply lose access to protected documents and messages after three months.
Even if the trial RMS service were guaranteed to go on forever, there is still a good reason why you should use your own RMS server rather than the free one. Remember that part of RMS’s job is to authenticate each user’s identity. In the Exchange Server 2007 implementation of RMS, this is done at the Hub Transport server level. In the free version of RMS, Microsoft uses Microsoft Passports as the means of identifying users.
The reason why this is such a big deal is because Microsoft Passports are completely outside of your control. You have no way of centrally managing Microsoft Passports or of requiring your users to use a standard passport name. Besides that, there are so many people in the world using Microsoft Passports, that it would be easy to inadvertently assign permissions to the incorrect person by making a typo.
There is one thing about the free version of RMS that is better than the commercial version. The free version is global in nature. If you wanted to send a rights protected message to a recipient who works for another company, there is nothing stopping you from doing so, as long as you both have Microsoft Passports and are registered with Microsoft’s RMS trial program.
The Windows Server 2008 version of AD RMS also allows you to send rights protected messages to recipients outside of your Exchange organization, but doing so is much more complicated. In order to accomplish this, both organizations must have AD RMS servers in place, and you must use Active Directory Federation Services (AD FS) to establish a relationship between the two organizations. Only then can you send rights protected messages between the two organizations.
Assuming that you choose to use the commercial version of Rights Management Services, you may have to install a client component. As you may recall, earlier I mentioned that AD RMS would not work unless you installed a client component onto the Hub Transport server. This same client component is also required for any computer that will be using Outlook to send or receive protected messages.
The good news is that if your workstations are running Windows Vista then you already have everything that you need, because the client component for RMS is installed by default. If you have workstations that are running Windows XP, then you will need the SP2 version of the Windows Rights Management Services Client. I provided a link to the 64-bit version earlier in this article, but if you need the 32-bit version, you can download it at: Microsoft Windows Rights Management Services Client with Service Pack 2 – x86
Conclusion
In this article, I have explained that configuring Exchange Server 2007 to support rights management is a fairly simple process, although there are a number of prerequisites that must be met. If you need additional assistance with the initial deployment and configuration of AD RMS in Windows Server 2008 then I recommend checking out my book The Real MCTS / MCITP Upgrading Your MCSA on Windows Server 2003 to Windows Server 2008 (Syngress ISBN 978-1-59749-236-2). The book is designed to serve as a study guide for Microsoft’s 70-648 certification exam, but it covers AD RMS deployment step by step.

Load comments