*Update at the end
Azure Storage Policies are around for some time already, but they manage to stay unnoticed. This feature is very powerful and few people know about it.
Probably you already know about Storage Keys and Shared Access Security. It’s important to highlight one limitation: Once we generate a SAS key, we can’t change or cancel it anymore.
The SAS keys are not stored on the server side. Once they are generated, the server has no control over it and we can’t block it or make any change.
Very few people know there is a solution for this: Azure Storage Policies. The process is very simple. You create a Storage Policy for your container. You create a SAS key based on the storage policy and the magic is done. The policy is a server object which give you control over the generated SAS keys.
Creating and Testing a Storage Policy
Let’s follow some steps and test this concept.
1) Locate a file in a private blob container on your Azure subscription
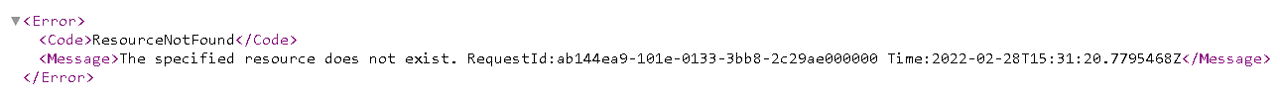
2) Try to open the file URL. You can’t, unless you provide authentication. We will do this with a SAS key.
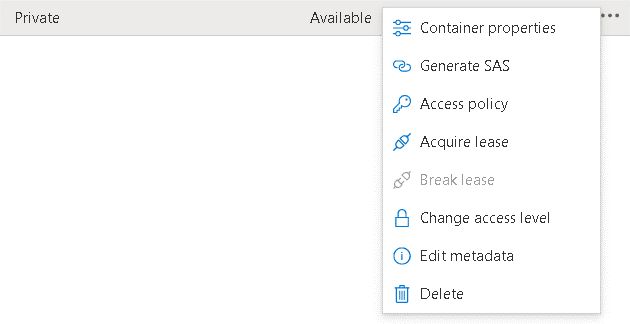
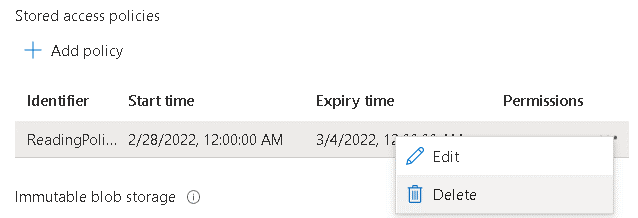
3) On the container, click “…” to open the menu and click Access Policies
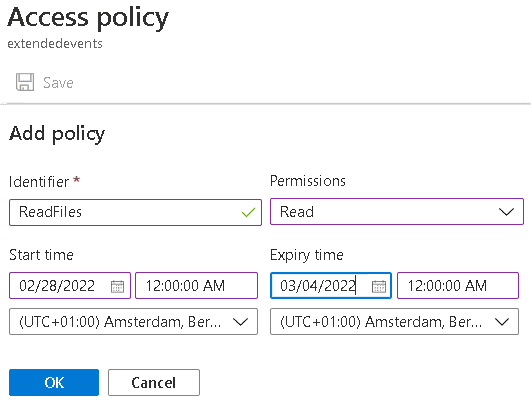
4) Configure the permission, start date and expiration date
This was the easy part. The next step is to create the SAS key based on the storage policy. You can’t do this through the portal. You can use Powershell to create the key or use Azure Storage Explorer. The Azure Portal doesn’t implement this feature. This explains a lot why this feature goes unnoticed.
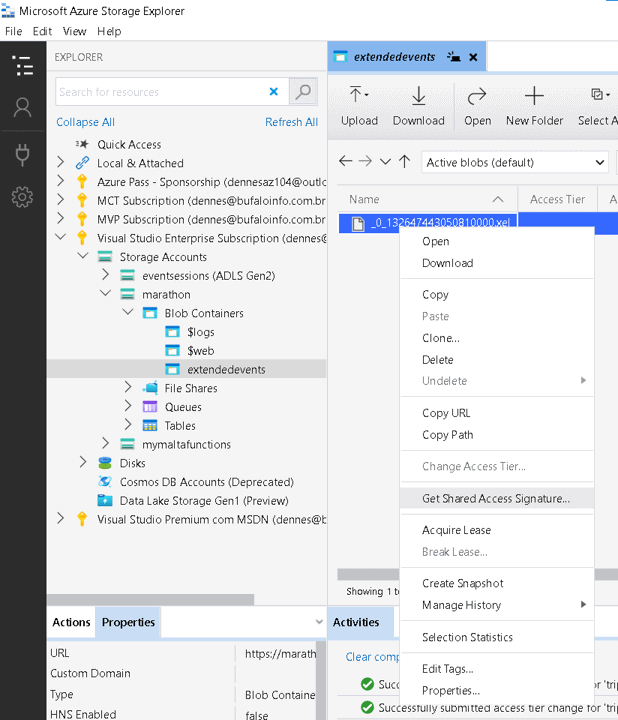
5) On Azure Storage Explorer, right click the file and select the option called Generate Shared Access Signature. The resulting window allows you to choose an existing Azure Policy to tie the key with.
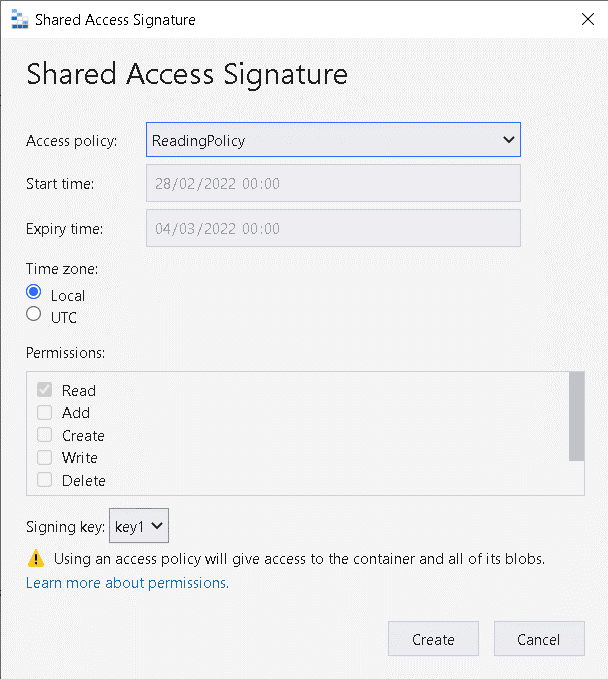
6) Click Create button to generate the key.
The resulting key is different than the usual SAS keys. It doesn’t include the parameters for the expiration date and the user permission. It includes a reference to the policy and it will use the information it has.
This enables you to manage many different scenarios for the generated SAS keys:
- Modify the user permission in the SAS keys
- Change the expiration date in the SAS keys
- Disable the SAS keys – by dropping the policy
Let’s complete some final tests to illustrate this:
7) Try to download the file using the generated link. You will be able to download it.
8) On the portal, delete the storage policy.
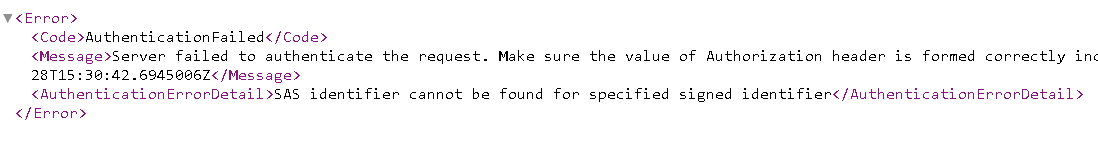
9) Try to download the file again. You may need to use an anonymous window to avoid cache. You will receive an authentication error.
Limitations
The Storage Account policies are created on the level of the container. You can control the user permission, but you can’t control the granularity. The use will have access to the entire container.
The policies are available for blob containers only, they can’t be created on file shares.
Summary
Storage Account Policy is a hidden feature which enables us to do what most people believe not being possible: Manage SAS keys from the server side.
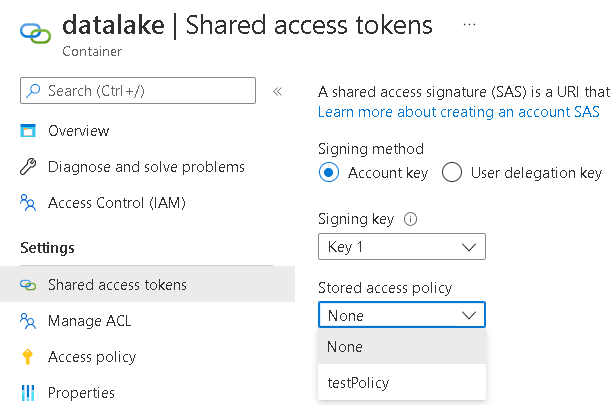
UPDATE 22/05: When I wrote this blog the policies could only be used in Azure Storage Explorer. Some weeks later, a new option became available on the Azure portal, allowing us to use the policies with SAS keys generated in the portal.



Load comments